Hamid.
AI-Based Blockchain & Offensive Security Learner
Exploring the intersection of offensive security, AI systems, and digital psychology. Founder of Linxploit — a cybersecurity initiative built for the next generation of ethical hackers.

AI-Based Blockchain & Offensive Security Learner
Exploring the intersection of offensive security, AI systems, and digital psychology. Founder of Linxploit — a cybersecurity initiative built for the next generation of ethical hackers.


A relentless explorer at the intersection of artificial intelligence, blockchain security, and offensive cyber operations. I approach security not as a profession — but as a goal.
From reverse engineering hardware with Flipper Zero to weaponizing AI for red-team operations, my work pushes the boundaries of what ethical hacking can achieve in a digitally weaponized world.
Beyond the technical, I study dark psychology, human behavioral manipulation, and the strategic warfare of the mind — because the greatest vulnerability in any system is always human.
Domains of expertise built through hands-on research and real-world application.
Network defense, threat modeling, vulnerability assessment and security architecture design.
Exploitation frameworks, payload crafting, privilege escalation, and post-exploitation techniques.
Full-scope pentest methodology, web application testing, and infrastructure assessments.
Open-source intelligence gathering, footprinting, digital forensics, and target profiling.
Adversarial ML, AI red-teaming, prompt injection, model extraction and AI threat vectors.
Smart contract auditing, DeFi exploit analysis, consensus attacks, and Web3 vulnerabilities.
TCP/IP, packet analysis, MITM attacks, protocol exploitation, and network forensics.
Kali, BlackArch, system hardening, kernel exploits, privilege escalation, and scripting.
Dark psychology, social engineering, behavioral profiling, manipulation detection, and influence ops.

Linxploit is a cybersecurity initiative built on the philosophy that understanding the attacker is the only true defense.
We operate at the bleeding edge of offensive security research, vulnerability discovery, and digital threat intelligence — delivering clarity in a world of evolving cyber threats.
Classified research and operational tools.
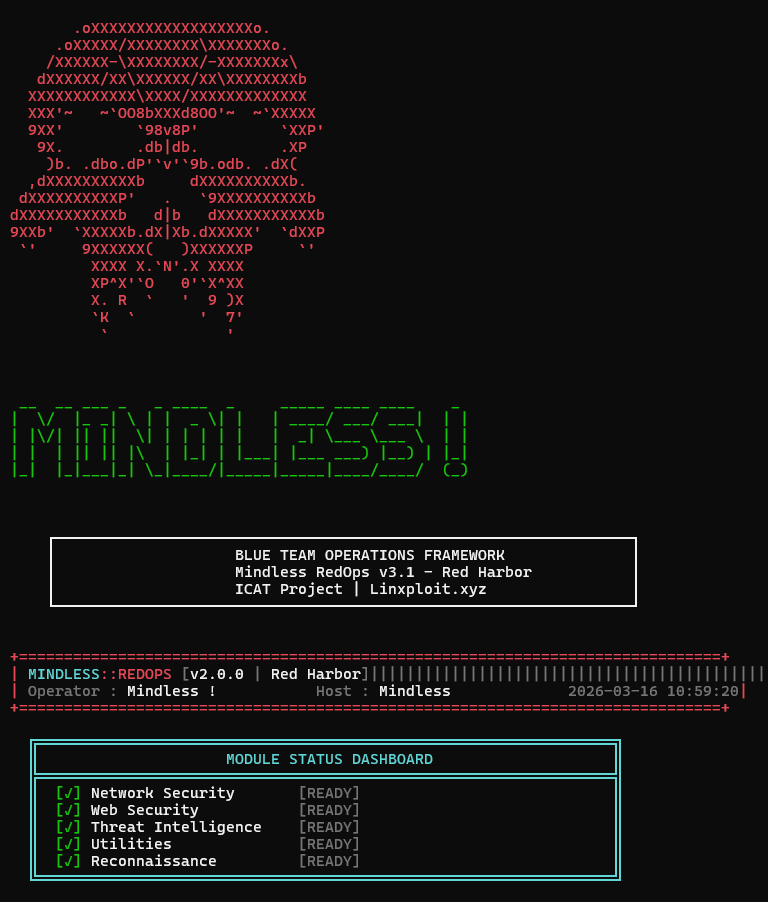 SECURITY FRAMEWORK
SECURITY FRAMEWORK
Flask-based cybersecurity platform centralizing red-team and reconnaissance utilities into a single web interface with modular architecture.
GitHub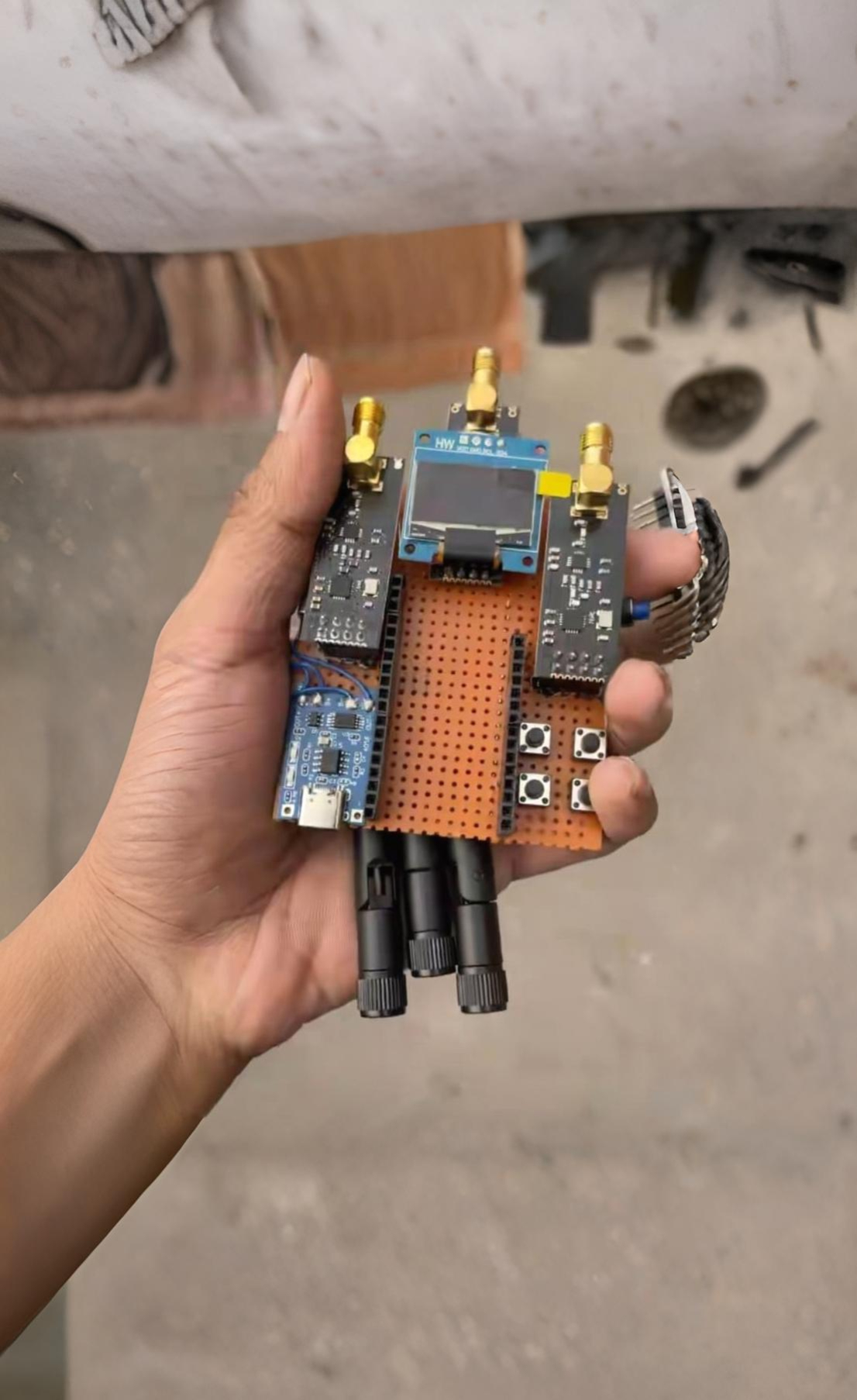 IoT SECURITY
IoT SECURITY
Wireless security and network testing tools built with ESP32/ESP8266 for portable IoT security research and wireless protocol exploration.
View Details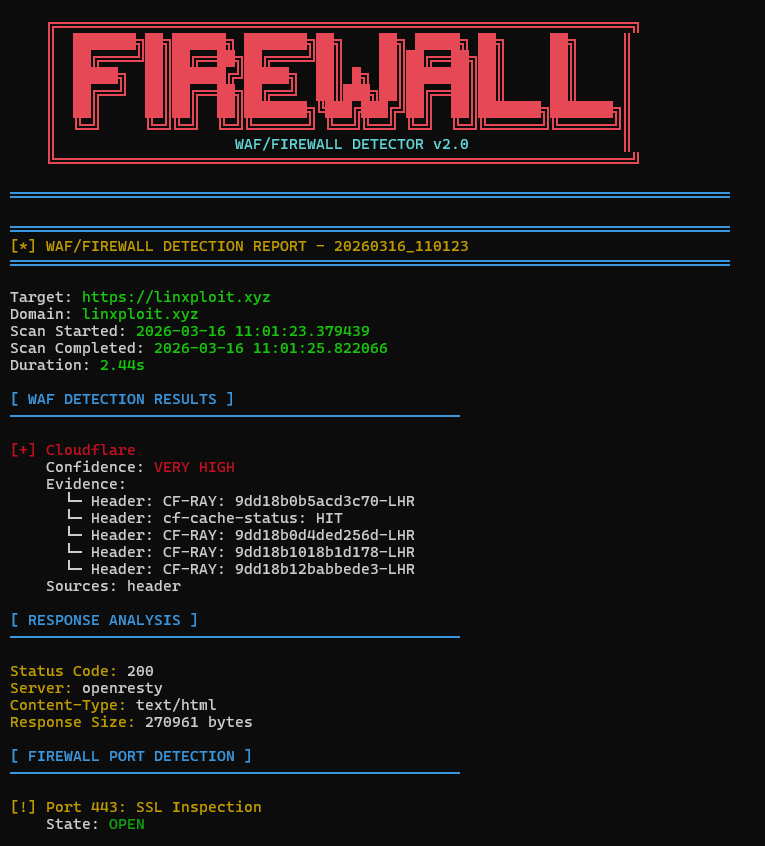 SECURITY SCANNER
SECURITY SCANNER
Identifies whether a target website is protected by a Web Application Firewall by analyzing HTTP responses, headers, and filtering behavior.
View Details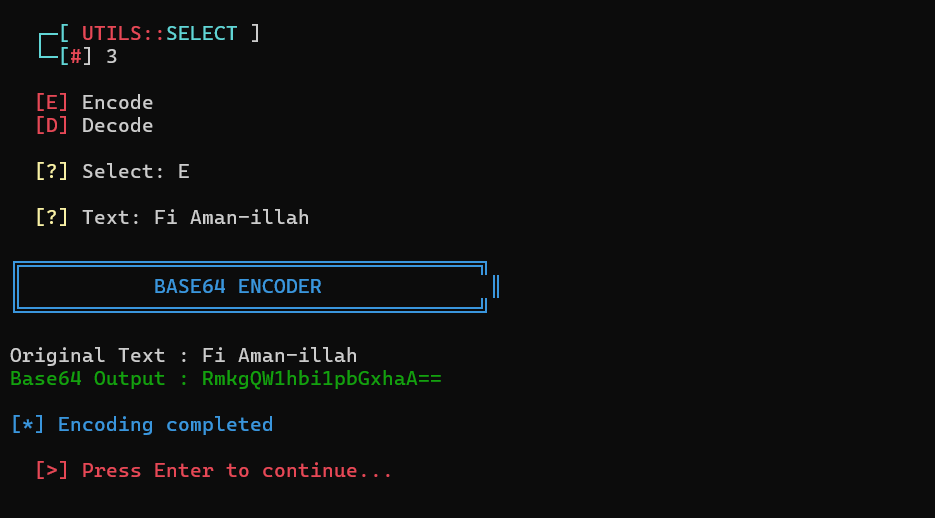 ENCODING TOOL
ENCODING TOOL
Encodes and decodes data using the Base64 scheme, commonly used in web technologies, authentication headers, and data transmission.
View Details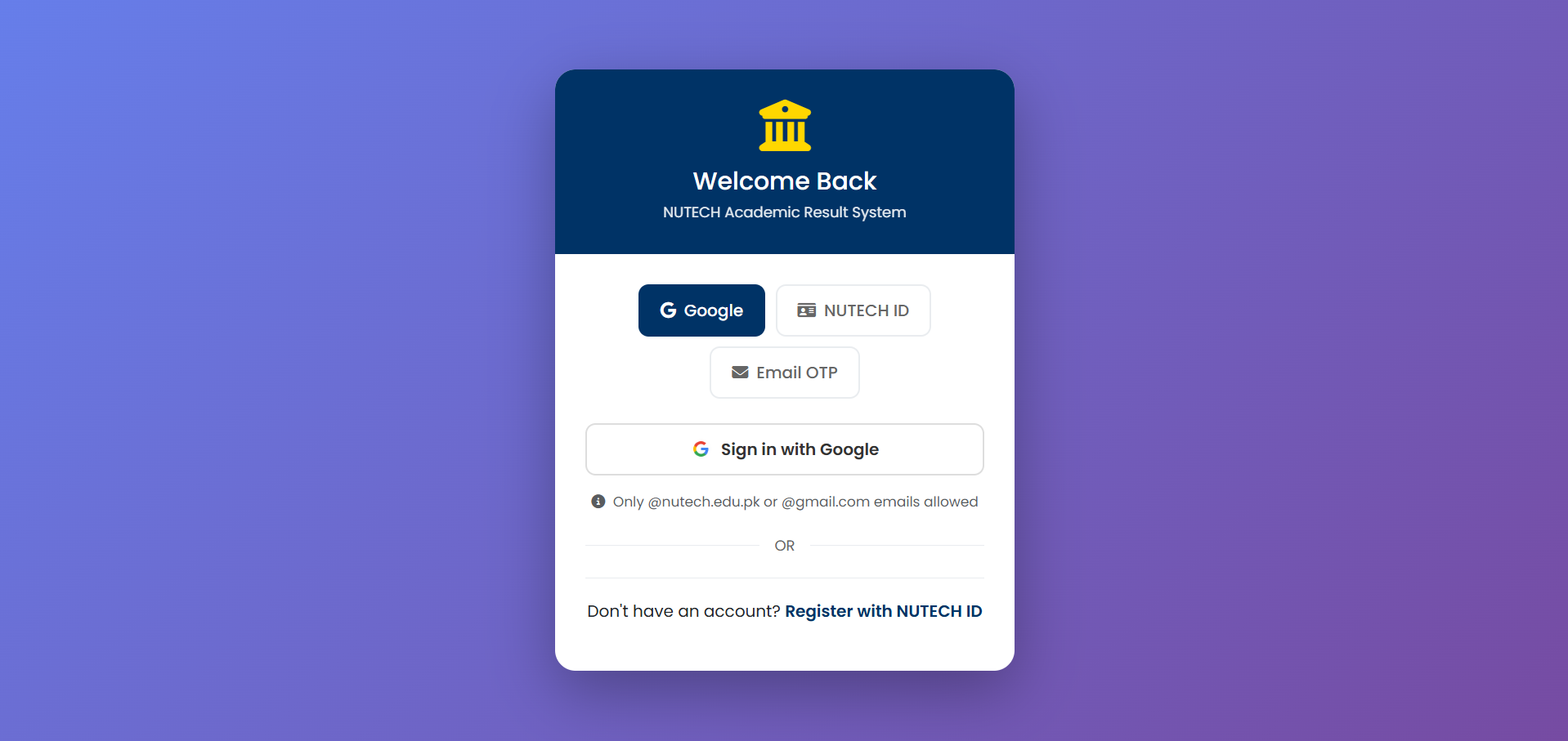 Databases
Databases
NUTECH Academic Result Management System - A secure, multi-login (Google, NUTECH ID, Email OTP) platform with role-based dashboards for students and teachers, featuring result entry, GPA/CGPA calculation, PDF transcripts, and management across 5 departments with 8 semesters.
View Details RECON TOOL
RECON TOOL
Discovers hidden directories and files on web servers by sending automated requests using wordlists to map potential attack surfaces.
View Details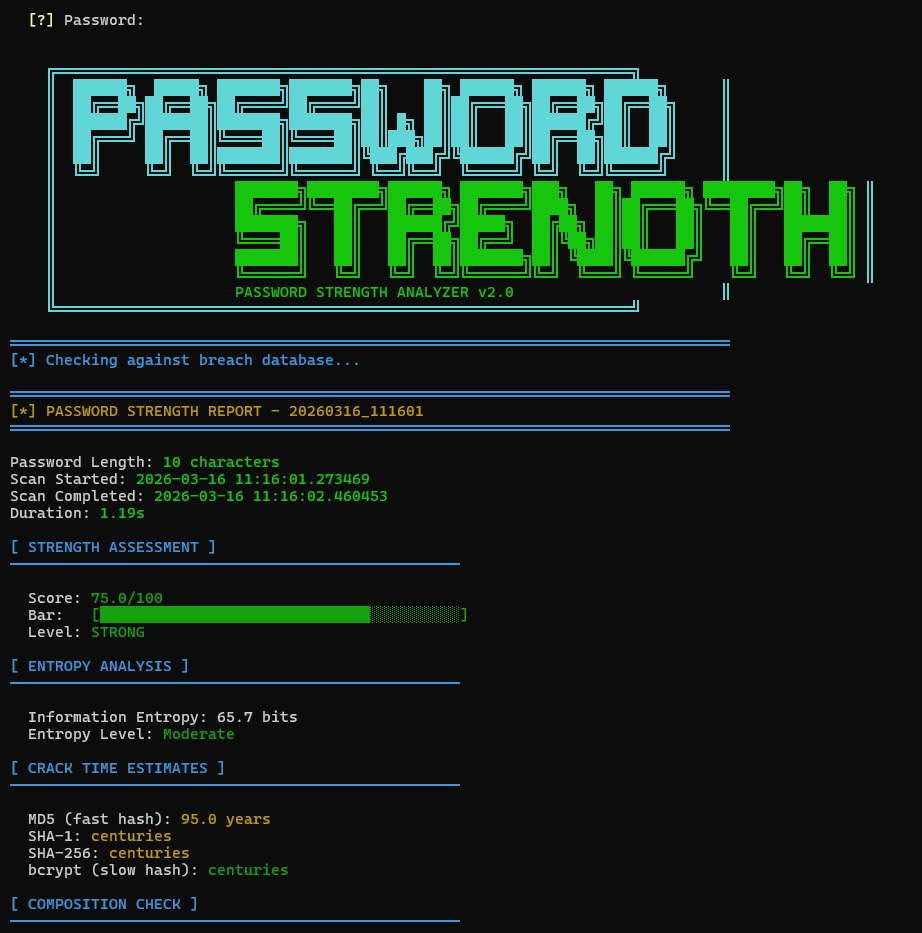 SECURITY TOOL
SECURITY TOOL
Analyzes password complexity and entropy to evaluate resistance against brute-force and dictionary attacks.
View Details THREAT DETECTION
THREAT DETECTION
Detects and flags potentially malicious URLs by analyzing patterns, domain characteristics, and known phishing indicators.
View Details NETWORK SCANNER
NETWORK SCANNER
Scans target hosts to identify open ports and active services, helping analyze network exposure during security assessments.
View Details SECURITY SCANNER
SECURITY SCANNER
Inspects SSL/TLS configurations to detect weak ciphers, certificate issues, and potential encryption vulnerabilities.
View Details WEB DEPLOY
WEB DEPLOY
Collection of live websites and platforms: linxploit.xyz, baghi.linxploit.com, and various sub-projects serving security research and services.
Visit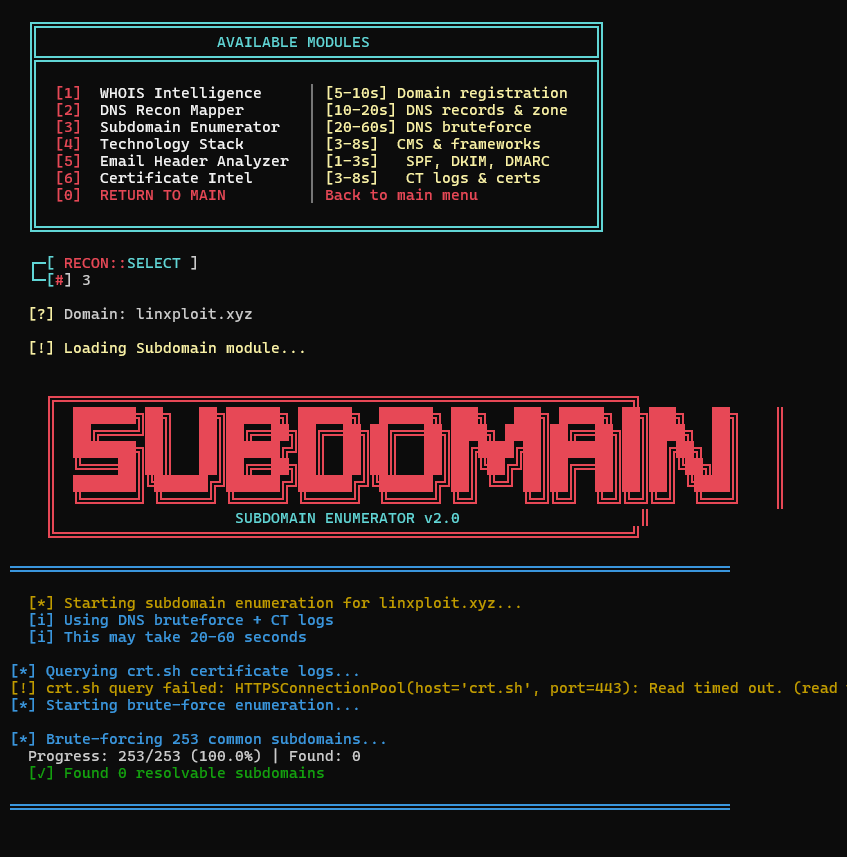 RECON TOOL
RECON TOOL
Enumerates subdomains associated with a target domain using automated discovery to expand the attack surface map.
View Details WIRELESS TOOL
WIRELESS TOOL
A wireless reconnaissance utility designed to monitor nearby Wi-Fi networks and collect technical information about access points and devices.
View Details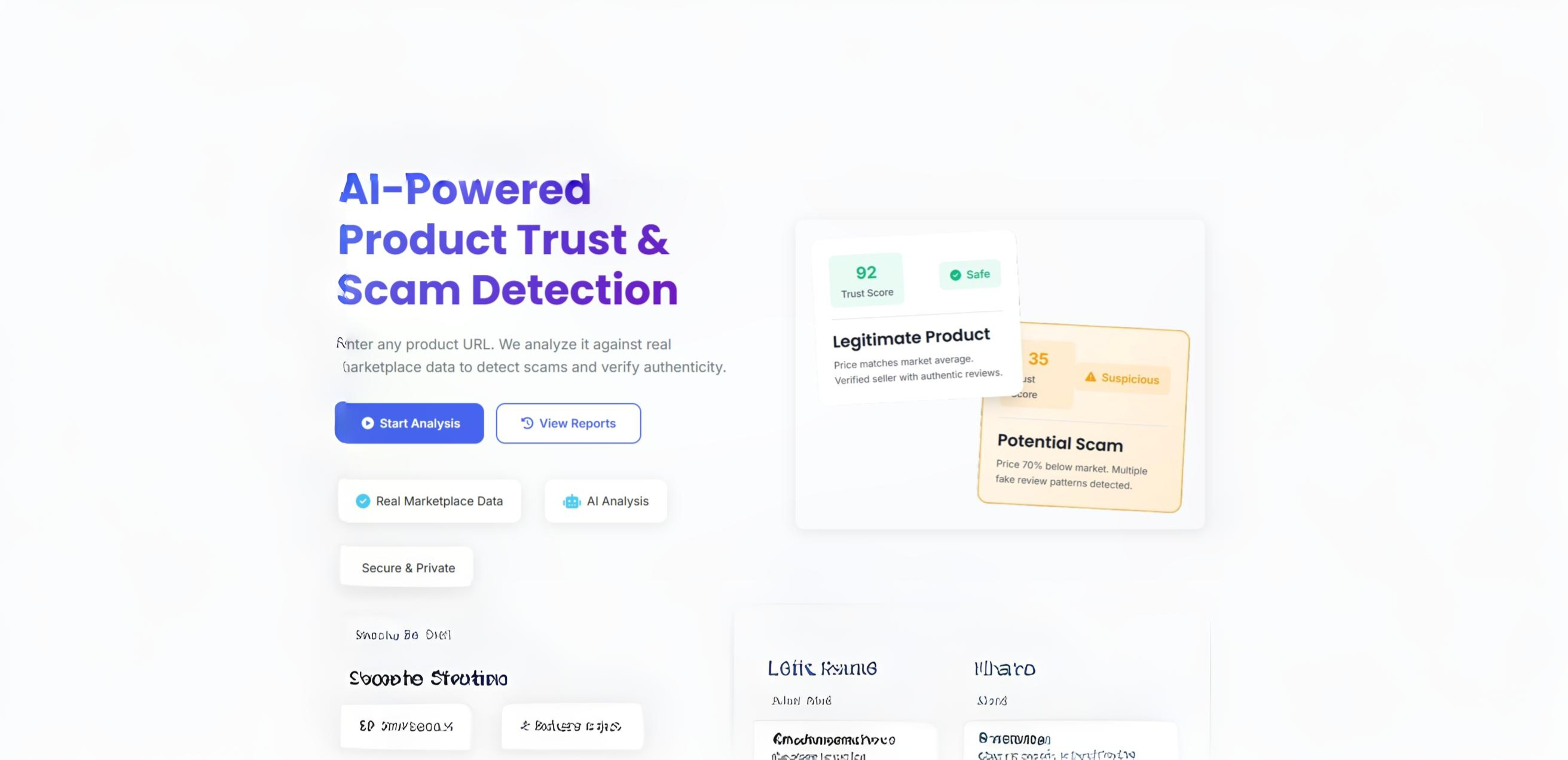 AI APPLICATION
AI APPLICATION
AI-driven system analyzing and evaluating product trustworthiness through automated decision-making and intelligent analysis engine.
Live Demo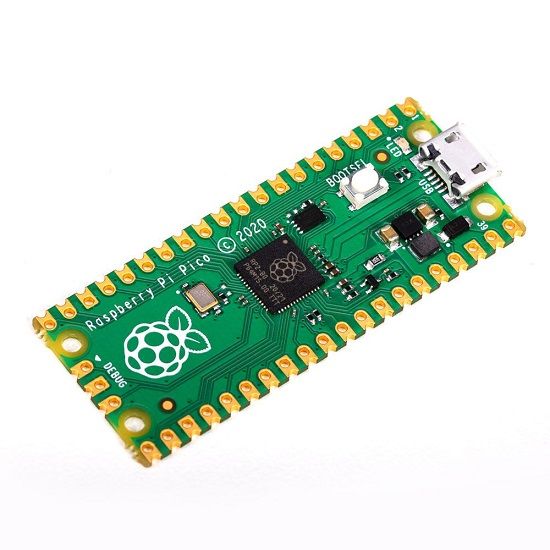 HARDWARE
HARDWARE
Raspberry Pi Pico RP2040-based USB HID emulator for keystroke injection and BadUSB security research with custom payload scripting.
View Details Operating System
Operating System
ZARI OS — A Debian-based system built for offensive security, speed, and control.
Coming SoonOpen to collaborations, red-team engagements, research discussions, and security consulting.